Getty Images
Pro-Russian threat actors are continuing their unrelenting pursuit of Ukrainian targets, with an array of campaigns that include fake Android apps, hack attacks exploiting critical vulnerabilities, and email phishing attacks that attempt to harvest login credentials, researchers from Google said.
One of the more recent campaigns came from Turla, a Russian-speaking advanced persistent threat actor that’s been active since at least 1997 and is among the most technically sophisticated in the world. According to Google, the group targeted pro-Ukrainian volunteers with Android apps that posed as launchpads for performing denial-of-service attacks against Russian websites.
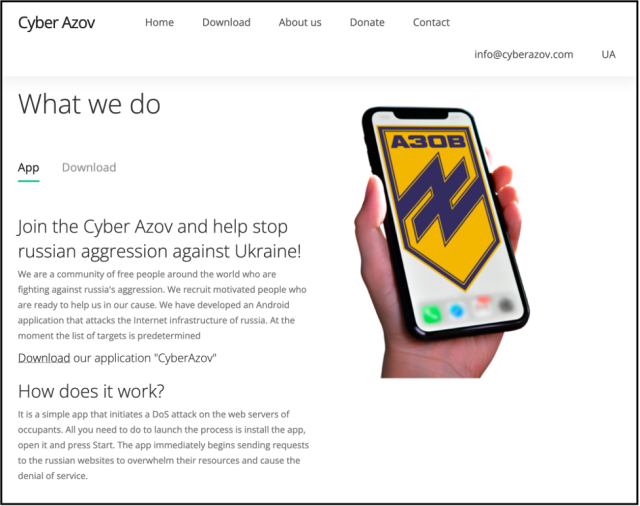
“All you need to do to launch the process is install the app, open it and press start,” the fake website promoting the app claimed. “The app immediately begins sending requests to the Russian websites to overwhelm their resources and cause the denial of service.”
In fact, a researcher with Google’s threat analysis group said, the app sends a single GET request to a target website. Behind the scenes, a different Google researcher told Vice that the app was designed to map out the user’s Internet infrastructure and “work out where the people that are potentially doing these sorts of attacks are.”
The apps, hosted on a domain spoofing the Ukrainian Azov Regiment, mimicked another Android app Google first saw in March that also claimed to perform DoS attacks against Russian sites. Unlike the Turla apps, stopwar.apk, as the latter app was named, sent a continuous stream of requests until the user stopped them.
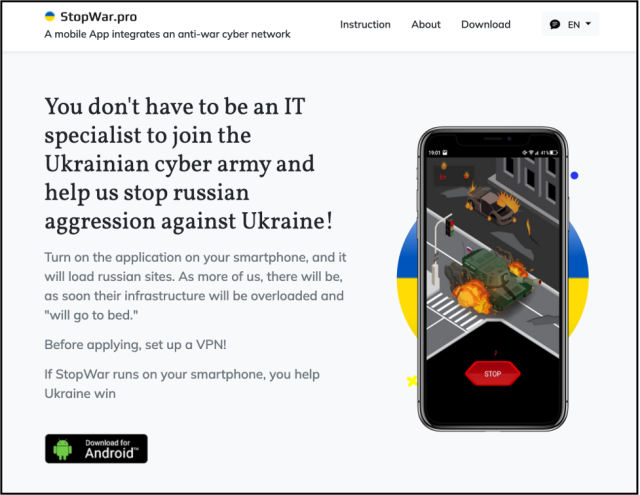
“Based on our analysis, we believe that the StopWar app was developed by pro-Ukrainian developers and was the inspiration for what Turla actors based their fake CyberAzov DoS app off of,” Google researcher Billy Leonard wrote.
Other hacking groups sponsored by the Kremlin have also targeted Ukrainian groups. Campaigns included the exploitation of Follina, the name given to a critical vulnerability in all supported versions of Windows that was actively targeted in the wild for more than two months as a zero-day.
Google researchers confirmed a CERT-UA report from June that said a different Kremlin-sponsored hacking group—tracked under a variety of names including Fancy Bear, known as Pawn Storm, Sofacy Group, and APT28—was also exploiting Follina in an attempt to infect targets with malware known as CredoMap. Additionally, Google said that Sandworm—yet another group sponsored by the Russian government—was also exploiting Follina. That campaign used compromised government accounts to send links to Microsoft Office documents hosted on compromised domains, primarily targeting media organizations in Ukraine.
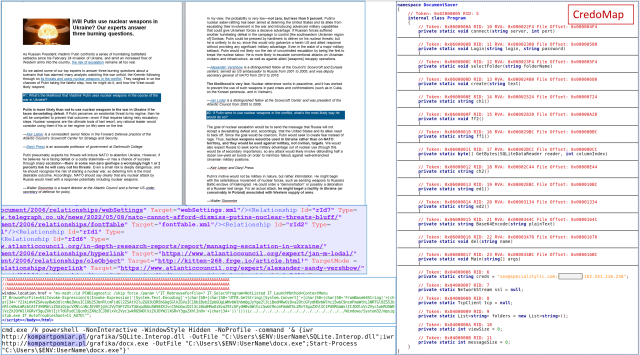
CERT-UA
Security firm Palo Alto Networks, meanwhile, reported on Tuesday that Russia’s Cloaked Ursa hacking group (also known as APT29, Nobelium, and Cozy Bear) had also stepped up malware attacks since the start of Russia’s invasion of Ukraine, in part by making malicious files for download available on Dropbox and Google Drive. US and UK intelligence services have publicly attributed APT29 to Russia’s Foreign Intelligence Service (SVR).
“This aligns with the group’s historic targeting focus, dating back to malware campaigns against Chechnya and other former Soviet bloc countries in 2008,” Palo Alto Networks researchers Mike Harbison and Peter Renals wrote. More recently, APT29 has been linked to a hack of the US Democratic National Committee discovered in 2016 and the SolarWindows supply-chain attacks from 2020.
Not all the threat groups targeting Ukraine are Kremlin-sponsored, Google said. Recently, a financially motivated actor tracked as UAC-0098 impersonated the State Tax Service of Ukraine and delivered malicious documents that attempted to exploit Follina. Google said the actor is a former initial ransomware access broker that previously worked with the Conti ransomware group.
On Wednesday, the US Cyber Command shared technical details related to what the agency said are several types of malware targeting Ukrainian entities in recent months. The malware samples are available on VirusTotal, Pastebin, and GitHub. Security firm Mandiant said two separate espionage groups used the malware, one tracked as UNC1151 and attributed by Mandiant to the Belarusian government and the other tracked as UNC2589, which the firm said is “believed to act in support of Russian government interest and has been conducting extensive espionage collection in Ukraine.”
The European Union also called out the Russian government this week, noting that a recent distributed denial-of-service campaign was only the latest example of cyberattacks it launched since its invasion.
“Russia’s unprovoked and unjustified military aggression against Ukraine has been accompanied by a significant increase of malicious cyber activities, including by a striking and concerning number of hackers and hacker groups indiscriminately targeting essential entities globally,” EU officials wrote. “This increase in malicious cyber activities, in the context of the war against Ukraine, creates unacceptable risks of spillover effects, misinterpretation, and possible escalation.”